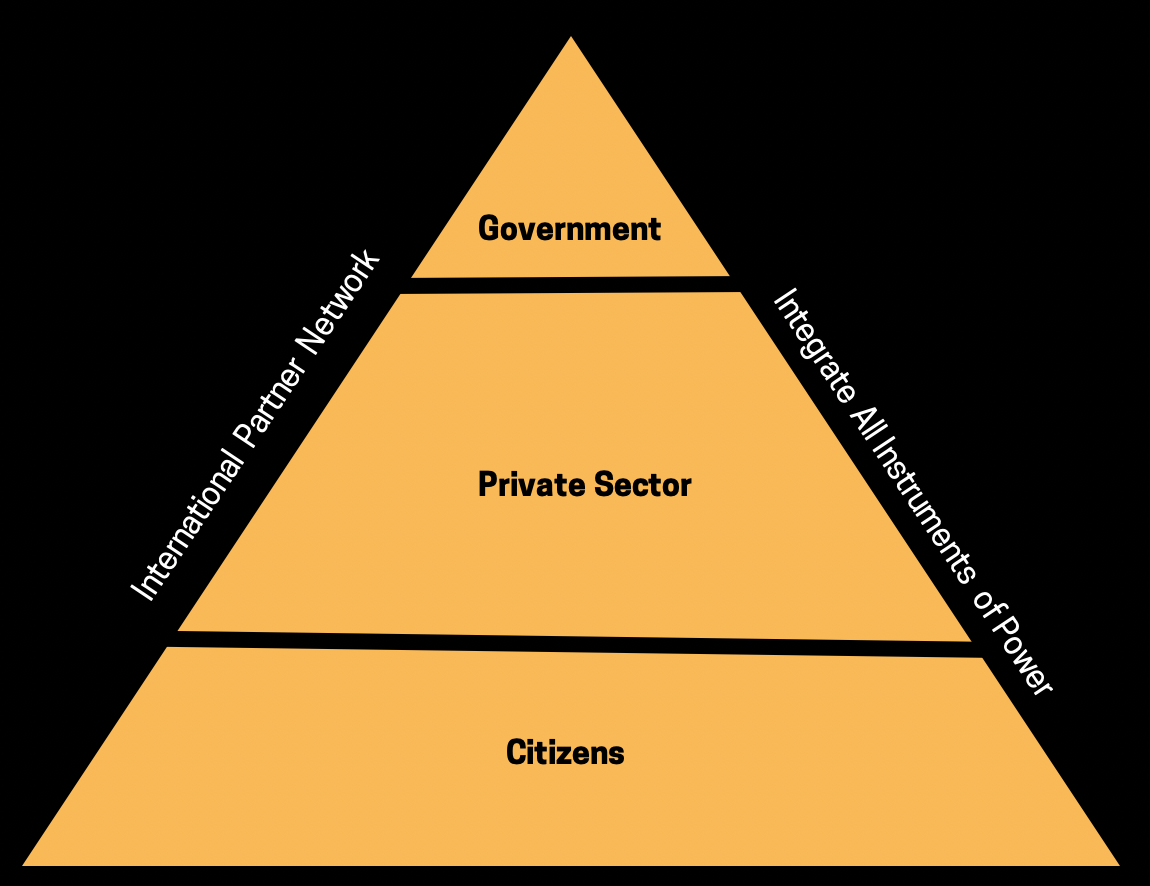
We've mentioned layered cyber deterrence before, but this new strategy combines a number of traditional deterrence mechanisms and extends them beyond the government to develop a whole-of-nation approach. The key for success is collaboration between the private and public sectors to build national resilience and reshape the cyber ecosystem in a way that increases security, while imposing costs against malicious actors.
Layered cyber deterrence works in three ways:
- Combining traditional methods of altering the cost-benefit calculus of adversaries with forms of influence optimized for a connected era, such as promoting norms that encourage restraint and incentivize responsible behavior in cyberspace. Collaboration in a connected world strengthens the ecosystem, but it requires international engagement and collaboration with the private sector.
- Emphasizing working with the private sector to efficiently coordinate how the nation responds with speed and agility to emerging threats. This strategy emphasizes the need for the federal government to work with state and local authorities to help fund and solve the challenge of enemies attacking the networks on which everyone relies on.
- The US is prepared to impose costs to deter conflict, limit malicious adversary behavior below the level of armed conflict. "Defend forward" is an important part of this layer — rather than reacting to attacks, the US should shift to proactively observing, pursuing, and countering adversary operations and imposing costs to change adversary behavior.
The central idea is simple: increase the costs and decrease the benefits that adversaries anticipate when planning cyberattacks against American interests.
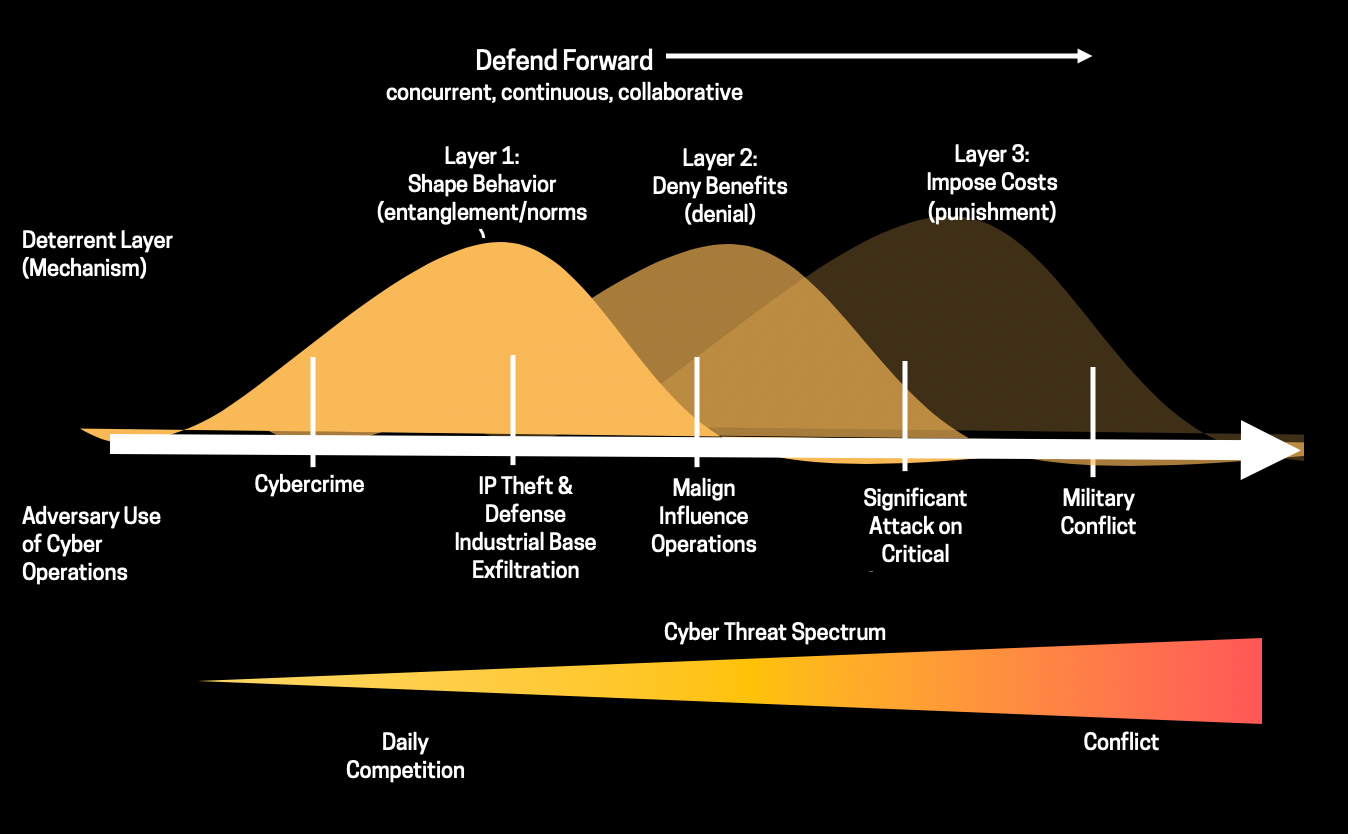
This can be achieved by employing multiple deterrent mechanisms concurrently, continuously, and collaboratively across the public and private sectors. The three layers:
- Shape Behavior: US and allies collectively develop and implement cyber norms based on shared interests and values
- Deny Benefits: US government collaborates with the private sector to reduce vulnerabilities and deny benefits to adversaries. The strategy is to force adversaries to make difficult choices regarding resources, access, and capabilities.
- Impose Costs: US will be prepared to impose costs to deter conflict, limit malicious adversary behavior, and if necessary, prevail in war by employing the full spectrum of its capabilities. "Defending forward" is an important part of the imposition layer; the US government must demonstrate its ability to impose costs using all instruments of power.
Challenges with implementing deterrence:
- Deterring state must clearly communicate the terms of a threat so that the target understands the behavior expected of it and the potential consequences of ignoring the threat
- The deterrer should ensure that the threatened costs inflicted adversary outweigh the latter's perceived benefits from conducting the undesired action
- Deterrent threats must be credible. The target of deterrence must perceive that costs will actually be imposed
- Deterrent threats should be coupled with some form of reassurance to the target that if it complies and does not act, the deterrer will refrain from carrying out the threatened response
Although deterrence is an enduring American strategy, it must be adapted to address how adversaries leverage new technology and connectivity to attack the US.
Layered cyber deterrence is the way forward. It is the best way for the government to implement new authorities and take appropriate proportional action that builds national resilience as well as disrupts, defeats, and deters active cyber campaigns, including those targeting critical economic and political institutions like election systems.
ABOUT STRATEGIC CYBER VENTURES
Cybersecurity is national security, and we're a D.C.-based venture capital firm on a mission to find cutting-edge startups that help us make an impact. We go beyond the check to help our founders win by leveraging our industry connections and experience as cybersecurity veterans to fuel their companies from inception to exit.
To learn more about our investment strategy and portfolio, explore www.scvgroup.com or connect with us on X @SCV_Cyber to be part of our mission in shaping the future of cybersecurity.
